Difference between revisions of "KHIKA App for Seqrite Utm Firewall"
Onkar pawar (talk | contribs) (→Adding the device in the Adaptor) |
Onkar pawar (talk | contribs) |
||
| Line 55: | Line 55: | ||
Wait for a few minutes for changes to apply and data to arrive in kHIKA. With all these steps, we should now expect the data to arrive in KHIKA. Lets discover some live data in KHIKA. | Wait for a few minutes for changes to apply and data to arrive in kHIKA. With all these steps, we should now expect the data to arrive in KHIKA. Lets discover some live data in KHIKA. | ||
| + | |||
| + | |||
| + | === Chekpoint Firewall Alerts === | ||
| + | |||
| + | Alerts are generated when certain critical behavior is observed in the system. Alerts can be monitored in real-time on Alerts Dashboard in KHIKA. Relevant stakeholders can also receive the alerts via emails. The table below explains all the pre-canned alerts shipped with KHIKA App for Checkpoint Firewall. | ||
| + | |||
| + | ==== Alerts Description ==== | ||
| + | |||
| + | {| class="wikitable" | ||
| + | |+ style="caption-side:bottom; color:#e76700;"|''Alert Details Table'' | ||
| + | |- | ||
| + | |'''Alert Name''' | ||
| + | |'''Description''' | ||
| + | |'''Suggested Resolution''' | ||
| + | |- | ||
| + | |Checkpoint firewall Possible data exfiltration | ||
| + | |This alert is triggered when large amount of data (more than 5 MB ) being sent to an external network. | ||
| + | |This alert is detected when a large amount of data is uploaded on external sites. This may be an attempt of data ex-filtration from the organisation. | ||
| + | Please check the real user associated with the source IP and the workstation from which the data upload happened. Verify if sensitive data was ex-filtrated. | ||
| + | |- | ||
| + | |Checkpoint firewall Checkpoint control log message | ||
| + | |This alert is triggered when action is ctl and internal message is generated by Checkpoint | ||
| + | |Checkpoint internal message is generated. Please check the documentation of Checkpoint and do the suggested action. | ||
| + | |- | ||
| + | |Checkpoint firewall Possible icmp probe | ||
| + | |This alert is triggered when high inbound icmp requests are made and are accepted | ||
| + | |ICMP probe is an old and established technique used by attackers as the first step that involves reconnaissance. This is used to check what IPs/Hosts are responding to the ping request so that further targeted can be launched on the responding IPs/Hots.<br/><br/> | ||
| + | The probing IP, if not a legitimate IP, ,it should be blocked at the periphery. | ||
| + | Check the reputation of the probing IP in external reputation databases, such as VirtusTotal.com or IPVoid.com etc. If the reputation is found to be dubious or bad, you must block such IPs. | ||
| + | |- | ||
| + | |Checkpoint firewall IPS bypassing | ||
| + | |This alert is triggered when IPS is bypassed. | ||
| + | |The firewall IPS mode is enabled by default in NextGen firewalls. However, sometimes the firewall runs out of its resources, such as CPU or Memory due sudden heavy load. In such cases, the firewall disables the IPS mode so that it can service the traffic traffic. Disabled IPS mode on the peripheral firewall is a compromised operating mode as an attacker can invade into your network by exploiting the lack of IPS service on your firewall. | ||
| + | |- | ||
| + | |Checkpoint firewall Worm detected | ||
| + | |This alert is triggered when traffic is generated on port 445,137,138,139 and communication direction is inbound | ||
| + | |Log messages indicative of a worm are detected. Check the attacking IPs in question. Verify the reputation these IPs in reputation databased such as virustotal.com, ipvoid.com etc. | ||
| + | |- | ||
| + | |Checkpoint firewall Backdoor activity detected | ||
| + | |This alert is triggered when traffic is generated from internal machine on vulnerable ports(3127,3198,6129,7080). | ||
| + | |This event indicates that a traffic is generated from internal machine on vulnerable ports(3127,3198,6129,7080). Typically, these ports are used by attacker to exploit vulnerable programs listening on these ports.<br/><br/> | ||
| + | Check is these ports are open and on what servers. Do you really need these ports opened? | ||
| + | Check what programs are running on these ports. Check vulnerability reports of the applications | ||
| + | Block these ports for external traffic, unless mandatory to keep them opened. | ||
| + | If you have to keep any of these ports opened, try to restrict the access to legitimate IPs. | ||
| + | If you get a suspicious IP repetitively trying to access these port, block the IP. Check the reputation of the IP on popular website such as ipvoid.com, virustotal.com etc. | ||
| + | |- | ||
| + | |Checkpoint firewall Communication with possible IOC or bad IP | ||
| + | |This alert is triggered when any one of the Source or Destination IP is found malicious with accepted action | ||
| + | |KHIKA shares community based threat intelligence (TI) every 24 hours. TI has list of IP addresses with bad reputation. Every bad IP is marked with number of communities reporting it, name of each community and confidence indicating how confident are we about the reputation. This alert is generated when communication with a bad IP is let through.<br/><br/> | ||
| + | If communication with a bad IP is happening, it must be blocked immediately as it could be a possible attack or data ex-filtration. | ||
| + | You can check how log this communication is happening by simply searching the malicious IP in the logs. You can also check what internal IP addresses are communicating with this IP addresses and track the real users behind those internal IP addresses. | ||
| + | Cross-check the reputation of the IP with popular websites such as ipvoid.com, virustotal.com | ||
| + | If you see an internal IP constantly getting involved in malicious communication (with same or multiple external IP addresses), you may install agents on the internal nodes involved and check the real user and process responsible for this communication. | ||
| + | It is critical to block this rogue communication. | ||
| + | |- | ||
| + | |Checkpoint firewall host scan activity by malicious ip | ||
| + | |This alert is triggered when same malicious ip is trying to generate traffic for one destination ip on more than 10 different ports within 1 minute and the request is denied. | ||
| + | |Bad ip address tries to spray connection requests on multiple popular ports (21,22,53,80,443 etc) targeting one single IP address at a time with an intention to find the open ports on the target IP address. Typically, scan attempt is the first stage of reconnaissance in the attack life cycle.<br/><br/> | ||
| + | It is important to check the reputation of the external ip address and block the same if necessary. | ||
| + | |- | ||
| + | |Checkpoint firewall successful host scan activity | ||
| + | |This alert is triggered when same source ip is trying to generate traffic for one destination ip on more than 10 different ports but all the time request is denied .After that same source ip attempts to connect to same destination on one more port and this time it successfully connects on that port. All this happen within 1 minute. | ||
| + | |Attacker tries to spray connection requests on multiple popular ports (21,22,53,80,443 etc) targeting one single IP addresses at a time with an intention to find the open ports on the target IP address. Typically, scan attempt is the first stage of reconnaissance in the attack life cycle and attacker done successful connection on open ports<br/><br> | ||
| + | It is important to check the reputation of the suspected ip address. | ||
| + | If the suspected ip address is external, you may consider blocking it. | ||
| + | If the suspected ip address is internal, you may need to verify the sanity of the corresponding device | ||
| + | It is also important to verify the sanity of affected internal nodes by checking if any unwarranted system policy change or software configuration/updates have occurred during the affected time period. If required, quarantine the affected servers till the time the issues are resolved. | ||
| + | This may be a false positive. | ||
| + | |- | ||
| + | |Checkpoint firewall successful host scan activity by malicious ip | ||
| + | |This alert is triggered when same malicious ip is trying to generate traffic for one destination ip on more than 10 different ports, but all the time request is denied .After that same malicious ip attempt to connect to same destination ip on one more port and this time it successfully connected on that port. All this happen within 1 minute. | ||
| + | |Bad ip address tries to spray connection requests on multiple popular ports (21,22,53,80,443 etc) targeting one single IP addresses at a time with an intention to find the open ports on the target IP address. Typically, scan attempt is the first stage of reconnaissance in the attack life cycle and attacker done successful connection on open ports<br/></br> | ||
| + | It is important to check the reputation of the external ip address and block the same if necessary. | ||
| + | It is also important to verify the sanity of affected internal nodes by checking if any unwarranted system policy change or software configuration/updates have occurred during the affected time period. If required, quarantine the affected servers till the time the issues are resolved. | ||
| + | |- | ||
| + | |Checkpoint firewall sweep scan attack by malicious ip | ||
| + | |This alert is triggered when same malicious ip is trying to generate traffic on more than 10 destination ip but all the time request is denied . All this happens within 1 minute. | ||
| + | |Attacker tries to spray connection requests on one of the popular ports (21,22,53,80,443 etc) on multiple IP addresses with an intention to find which ports are opened on what IP addresses. Typically, scan attempt is the first stage of reconnaissance in the attack life cycle and attacker done successful connection | ||
| + | Bad ip addresses tries to spray connection requests on one of the popular ports (21,22,53,80,443 etc) on multiple IP addresses with an intention to find which ports are opened on what IP addresses. Typically, scan attempt is the first stage of reconnaissance in the attack life cycle.<br/><br/> | ||
| + | It is important to check the reputation of the external ip address and block the same if necessary. | ||
| + | |- | ||
| + | |Checkpoint firewall successful sweep scan activity | ||
| + | |This alert is triggered when same source ip is trying to generate traffic on more than 10 destination ip but all the time request is denied .After that same source ip attempts to connect one more destination ip and this time it successfully connects. All this happen within 1 minute. | ||
| + | |Attacker tries to spray connection requests on one of the popular ports (21,22,53,80,443 etc) on multiple IP addresses with an intention to find which ports are opened on what IP addresses. Typically, scan attempt is the first stage of reconnaissance in the attack life cycle and attacker done successful connection on one of ip addresses | ||
| + | It is important to check the reputation of the suspected ip address. | ||
| + | If the suspected ip address is external, you may consider blocking it. | ||
| + | If the suspected ip address is internal, you may need to verify the sanity of the corresponding device | ||
| + | It is also important to verify the sanity of affected internal nodes by checking if any unwarranted system policy change or software configuration/updates have occurred during the affected time period. If required, quarantine the affected servers till the time the issues are resolved. | ||
| + | This may be a false positive. | ||
| + | |- | ||
| + | |Checkpoint firewall successful sweep scan activity by malicious ip | ||
| + | |This alert is triggered when same malicious ip is trying to generate traffic on more than 10 destination ip but all the time request is denied .After that same source ip attempts to connect to one more destination ip and this time it successfully connects. All this happen within 1 minute. | ||
| + | |Bad ip address tries to spray connection requests on one of the popular ports (21,22,53,80,443 etc) on multiple IP addresses with an intention to find which ports are opened on what IP addresses. Typically, scan attempt is the first stage of reconnaissance in the attack life cycle and attacker finds open port on one of ip addresses and is able to establish a connection. | ||
| + | It is important to check the reputation of the external ip address and block the same if necessary. | ||
| + | It is also important to verify the sanity of affected internal nodes by checking if any unwarranted system policy change or software configuration/updates have occurred during the affected time period. If required, quarantine the affected servers till the time the issues are resolved. | ||
| + | |- | ||
| + | |Checkpoint firewall communication with suspicious ip | ||
| + | |This alert is triggered when bytes are sent and received during communication with malicious ip within 1 minute. | ||
| + | |Communication with a bad IP is happening, it must be blocked immediately as it could be a possible attack or data ex-filtration. | ||
| + | You can check the log for this communication by simply searching the malicious IP in the logs. You can also check which internal IP addresses are communicating with this IP address and track the real users behind those internal IP addresses.<br/><br/> | ||
| + | If you see an internal IP constantly getting involved in malicious communication (with same or multiple external IP addresses), you may install agents on the internal nodes involved and check the real user and process responsible for this communication. | ||
| + | If required, quarantine the affected internal servers till the time the issues are resolved. | ||
| + | |- | ||
| + | |Checkpoint firewall large data sent outside | ||
| + | |This alert is triggered when large amount of data (more than 1 GB) being sent to an external network | ||
| + | |Large amount of data being sent to an external network could be an indication of data ex-filtration. | ||
| + | Check with the user or process which is responsible for the data being sent out and whether it was done for legitimate business reasons. This could be a false positive. | ||
| + | |||
| + | |||
| + | |} | ||
Revision as of 10:20, 18 July 2019
Contents
Introduction
Firewall form an important part of organisations’ networks and hence by monitoring your firewall is imperative. Seqrite UTM Firewall send the traffic and user activity related information in the form of logs over syslog protocol. KHIKA Data Aggregator is pre-configured with syslog services on port 514. The key parts to get here are :
- Enabling Syslog forwarding on the device
- Install the KHIKA App for Checkpoint Firewall
- Get data from your Checkpoint Firewall into KHIKA Aggregator
Enabling Syslog forwarding on the device
Verifying SYSLOG data collection
After you enable the syslog forwarding on the end device, you must verify if the logs are being really received by KHIKA Data Aggregator. Please refer here to understand how to verify syslogs on KHIKA Data Aggregator.
How to Install the KHIKA App for Seqrite UTM Firewall ?
It is assumed, that you have already configured KHIKA Data Aggregator in your environment. If not, please read how to configure KHIKA Data Aggregator and perform the pre-requisite steps.
This section explains how to pick and install the KHIKA application for Seqrite UTM Firewall - Seqrite UTM Firewall. Installing the application shall put together and activate the adapter (parser) that can handle Checkpoint Firewall data format, the dashboards and the alert rules preconfigured.
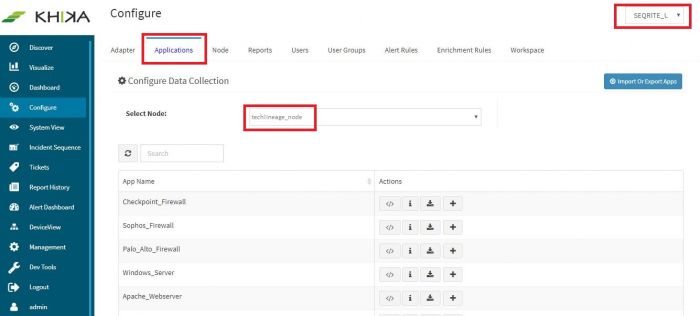
Go to “Applications” tab in the “Configure” menu.
Check whether the appropriate Workspace is selected. Note: Application is always loaded in a Workspace. Read the section on Workspaces to know more about KHIKA Workspaces. Also select your KHIKA aggregator name in the Node dropdown. This is to ensure that we are collecting data from the desired source and into the correct workspace which is ready with the configured application and components.
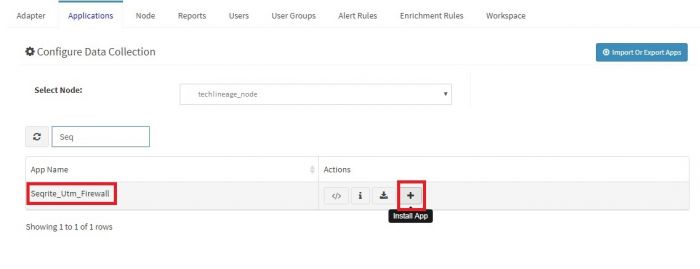
Click on the “+” button. A pop up appears.
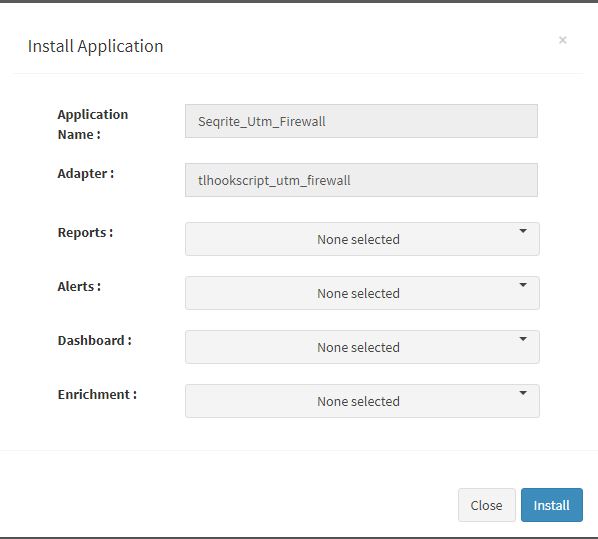
User can now select the contents of the application required. For example, on the dropdown for “Reports”, click to expand it. List of all reports can be seen. User can individually select the reports required by checking on the checkbox next to each. Alternatively, check on “Select All” option to get all of them. Similarly you can select contents from Alerts and Dashboards.
Visit the sections on KHIKA Reports, KHIKA Dashboards, KHIKA Alerts & Correlations to know more about these topics.
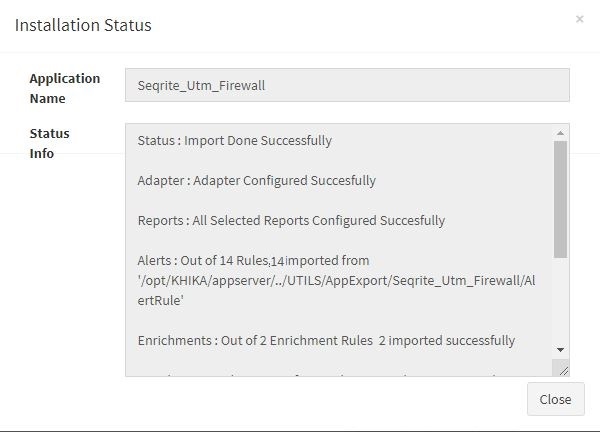
Click “OK” to proceed with the installation of the selected Application. After successful installation, following status should be displayed :
This simple procedure to install a KHIKA App, automatically configures the Adapter (required for parsing the data from raw syslogs), calculated KHIKA reports on raw data, Visualizations, Dashboards and Alerts – all in one click.
Adding the device in the Adaptor
After syslogs are enabled on the device and the App is installed into KHIKA, it is the time to add the device to the this App (in Adapter section of KHIKA Web GUI). Please refer here to know how to add the device to an App.
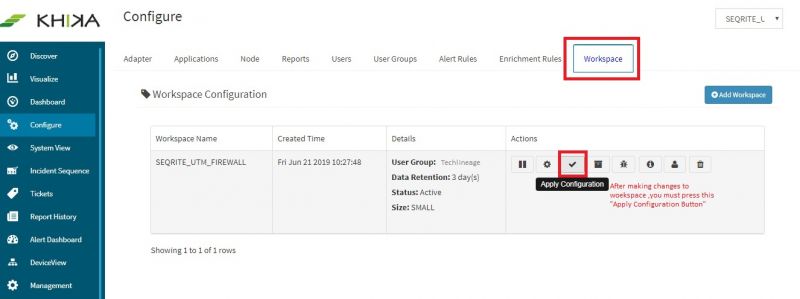
After making these configuration in KHIKA, you must apply these changes to the Workspace. Go to Configure, select the Workspace and in Workspace tab of configure menu press the Apply button as shown in the screenshot below.
Wait for a few minutes for changes to apply and data to arrive in kHIKA. With all these steps, we should now expect the data to arrive in KHIKA. Lets discover some live data in KHIKA.
Chekpoint Firewall Alerts
Alerts are generated when certain critical behavior is observed in the system. Alerts can be monitored in real-time on Alerts Dashboard in KHIKA. Relevant stakeholders can also receive the alerts via emails. The table below explains all the pre-canned alerts shipped with KHIKA App for Checkpoint Firewall.
Alerts Description
| Alert Name | Description | Suggested Resolution |
| Checkpoint firewall Possible data exfiltration | This alert is triggered when large amount of data (more than 5 MB ) being sent to an external network. | This alert is detected when a large amount of data is uploaded on external sites. This may be an attempt of data ex-filtration from the organisation.
Please check the real user associated with the source IP and the workstation from which the data upload happened. Verify if sensitive data was ex-filtrated. |
| Checkpoint firewall Checkpoint control log message | This alert is triggered when action is ctl and internal message is generated by Checkpoint | Checkpoint internal message is generated. Please check the documentation of Checkpoint and do the suggested action. |
| Checkpoint firewall Possible icmp probe | This alert is triggered when high inbound icmp requests are made and are accepted | ICMP probe is an old and established technique used by attackers as the first step that involves reconnaissance. This is used to check what IPs/Hosts are responding to the ping request so that further targeted can be launched on the responding IPs/Hots. The probing IP, if not a legitimate IP, ,it should be blocked at the periphery. Check the reputation of the probing IP in external reputation databases, such as VirtusTotal.com or IPVoid.com etc. If the reputation is found to be dubious or bad, you must block such IPs. |
| Checkpoint firewall IPS bypassing | This alert is triggered when IPS is bypassed. | The firewall IPS mode is enabled by default in NextGen firewalls. However, sometimes the firewall runs out of its resources, such as CPU or Memory due sudden heavy load. In such cases, the firewall disables the IPS mode so that it can service the traffic traffic. Disabled IPS mode on the peripheral firewall is a compromised operating mode as an attacker can invade into your network by exploiting the lack of IPS service on your firewall. |
| Checkpoint firewall Worm detected | This alert is triggered when traffic is generated on port 445,137,138,139 and communication direction is inbound | Log messages indicative of a worm are detected. Check the attacking IPs in question. Verify the reputation these IPs in reputation databased such as virustotal.com, ipvoid.com etc. |
| Checkpoint firewall Backdoor activity detected | This alert is triggered when traffic is generated from internal machine on vulnerable ports(3127,3198,6129,7080). | This event indicates that a traffic is generated from internal machine on vulnerable ports(3127,3198,6129,7080). Typically, these ports are used by attacker to exploit vulnerable programs listening on these ports. Check is these ports are open and on what servers. Do you really need these ports opened? Check what programs are running on these ports. Check vulnerability reports of the applications Block these ports for external traffic, unless mandatory to keep them opened. If you have to keep any of these ports opened, try to restrict the access to legitimate IPs. If you get a suspicious IP repetitively trying to access these port, block the IP. Check the reputation of the IP on popular website such as ipvoid.com, virustotal.com etc. |
| Checkpoint firewall Communication with possible IOC or bad IP | This alert is triggered when any one of the Source or Destination IP is found malicious with accepted action | KHIKA shares community based threat intelligence (TI) every 24 hours. TI has list of IP addresses with bad reputation. Every bad IP is marked with number of communities reporting it, name of each community and confidence indicating how confident are we about the reputation. This alert is generated when communication with a bad IP is let through. If communication with a bad IP is happening, it must be blocked immediately as it could be a possible attack or data ex-filtration. You can check how log this communication is happening by simply searching the malicious IP in the logs. You can also check what internal IP addresses are communicating with this IP addresses and track the real users behind those internal IP addresses. Cross-check the reputation of the IP with popular websites such as ipvoid.com, virustotal.com If you see an internal IP constantly getting involved in malicious communication (with same or multiple external IP addresses), you may install agents on the internal nodes involved and check the real user and process responsible for this communication. It is critical to block this rogue communication. |
| Checkpoint firewall host scan activity by malicious ip | This alert is triggered when same malicious ip is trying to generate traffic for one destination ip on more than 10 different ports within 1 minute and the request is denied. | Bad ip address tries to spray connection requests on multiple popular ports (21,22,53,80,443 etc) targeting one single IP address at a time with an intention to find the open ports on the target IP address. Typically, scan attempt is the first stage of reconnaissance in the attack life cycle. It is important to check the reputation of the external ip address and block the same if necessary. |
| Checkpoint firewall successful host scan activity | This alert is triggered when same source ip is trying to generate traffic for one destination ip on more than 10 different ports but all the time request is denied .After that same source ip attempts to connect to same destination on one more port and this time it successfully connects on that port. All this happen within 1 minute. | Attacker tries to spray connection requests on multiple popular ports (21,22,53,80,443 etc) targeting one single IP addresses at a time with an intention to find the open ports on the target IP address. Typically, scan attempt is the first stage of reconnaissance in the attack life cycle and attacker done successful connection on open ports It is important to check the reputation of the suspected ip address. If the suspected ip address is external, you may consider blocking it. If the suspected ip address is internal, you may need to verify the sanity of the corresponding device It is also important to verify the sanity of affected internal nodes by checking if any unwarranted system policy change or software configuration/updates have occurred during the affected time period. If required, quarantine the affected servers till the time the issues are resolved. This may be a false positive. |
| Checkpoint firewall successful host scan activity by malicious ip | This alert is triggered when same malicious ip is trying to generate traffic for one destination ip on more than 10 different ports, but all the time request is denied .After that same malicious ip attempt to connect to same destination ip on one more port and this time it successfully connected on that port. All this happen within 1 minute. | Bad ip address tries to spray connection requests on multiple popular ports (21,22,53,80,443 etc) targeting one single IP addresses at a time with an intention to find the open ports on the target IP address. Typically, scan attempt is the first stage of reconnaissance in the attack life cycle and attacker done successful connection on open ports It is important to check the reputation of the external ip address and block the same if necessary. It is also important to verify the sanity of affected internal nodes by checking if any unwarranted system policy change or software configuration/updates have occurred during the affected time period. If required, quarantine the affected servers till the time the issues are resolved. |
| Checkpoint firewall sweep scan attack by malicious ip | This alert is triggered when same malicious ip is trying to generate traffic on more than 10 destination ip but all the time request is denied . All this happens within 1 minute. | Attacker tries to spray connection requests on one of the popular ports (21,22,53,80,443 etc) on multiple IP addresses with an intention to find which ports are opened on what IP addresses. Typically, scan attempt is the first stage of reconnaissance in the attack life cycle and attacker done successful connection
Bad ip addresses tries to spray connection requests on one of the popular ports (21,22,53,80,443 etc) on multiple IP addresses with an intention to find which ports are opened on what IP addresses. Typically, scan attempt is the first stage of reconnaissance in the attack life cycle. |
| Checkpoint firewall successful sweep scan activity | This alert is triggered when same source ip is trying to generate traffic on more than 10 destination ip but all the time request is denied .After that same source ip attempts to connect one more destination ip and this time it successfully connects. All this happen within 1 minute. | Attacker tries to spray connection requests on one of the popular ports (21,22,53,80,443 etc) on multiple IP addresses with an intention to find which ports are opened on what IP addresses. Typically, scan attempt is the first stage of reconnaissance in the attack life cycle and attacker done successful connection on one of ip addresses
It is important to check the reputation of the suspected ip address. If the suspected ip address is external, you may consider blocking it. If the suspected ip address is internal, you may need to verify the sanity of the corresponding device It is also important to verify the sanity of affected internal nodes by checking if any unwarranted system policy change or software configuration/updates have occurred during the affected time period. If required, quarantine the affected servers till the time the issues are resolved. This may be a false positive. |
| Checkpoint firewall successful sweep scan activity by malicious ip | This alert is triggered when same malicious ip is trying to generate traffic on more than 10 destination ip but all the time request is denied .After that same source ip attempts to connect to one more destination ip and this time it successfully connects. All this happen within 1 minute. | Bad ip address tries to spray connection requests on one of the popular ports (21,22,53,80,443 etc) on multiple IP addresses with an intention to find which ports are opened on what IP addresses. Typically, scan attempt is the first stage of reconnaissance in the attack life cycle and attacker finds open port on one of ip addresses and is able to establish a connection.
It is important to check the reputation of the external ip address and block the same if necessary. It is also important to verify the sanity of affected internal nodes by checking if any unwarranted system policy change or software configuration/updates have occurred during the affected time period. If required, quarantine the affected servers till the time the issues are resolved. |
| Checkpoint firewall communication with suspicious ip | This alert is triggered when bytes are sent and received during communication with malicious ip within 1 minute. | Communication with a bad IP is happening, it must be blocked immediately as it could be a possible attack or data ex-filtration.
You can check the log for this communication by simply searching the malicious IP in the logs. You can also check which internal IP addresses are communicating with this IP address and track the real users behind those internal IP addresses. |
| Checkpoint firewall large data sent outside | This alert is triggered when large amount of data (more than 1 GB) being sent to an external network | Large amount of data being sent to an external network could be an indication of data ex-filtration.
Check with the user or process which is responsible for the data being sent out and whether it was done for legitimate business reasons. This could be a false positive.
|